Recent Activities
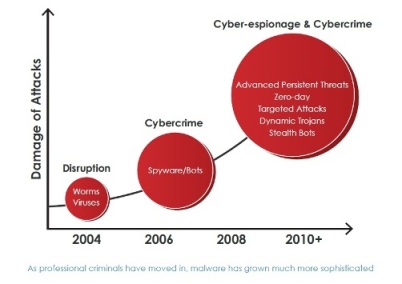
Malware innovations have been driven by attackers’ quests to gain increasing control of compromised computer systems and the networks in which they reside. Whether attackers use viruses, Trojans, bots or rootkits, today’s malware is designed for the long-term control of compromised machines. Often offensive tactics disrupt client-based security, like re-writing the Windows HOSTS file to disrupt antivirus signature and patch updates, or resetting Microsoft security updates to manual. Advanced malware also establishes outbound communications across several different protocols to upload stolen data and to download instructions and further malware payloads for other reconnaissance and malicious purposes.